Just think for a moment of a hacker breaking into someone’s account.
Did your mind instantly go to a place where someone is sitting behind a computer in a dark, smoke-filled room bashing away on a keyboard to gain access to your files?
Traditionally you’d be right but lately. a form of hacking known as social engineering has become more and more prevalent.
What is a Social Engineering Attack?
A Social Engineering attack is a well-orchestrated campaign against employees that employs a variety of digital, in-person or over the phone techniques to steal intellectual property, credentials or money.
Put simply, a hacker intercepts company information, some of which is freely available, creates an email address which looks like the one which belongs to the real boss, pops it off to the target in the finance department along with a fake invoice, and hits payday.
Isn’t there easier ways to get information?
Well hackers prefer Social Engineering because it’s much easier to hack a human than a business. Social Hacking Engineers play on human psychology to get their information rather than trying to navigate around increasingly strong computer systems. Why bother trying to mount a sophisticated technical hack when you could just pick up the phone and trick someone in a matter of minutes?
There are four mains ways that Social Engineering Occurs these being:
Phishing: Where a hacker uses email to trick someone into giving them access to some kind of account or login or financial information.
Vishing: The same as phishing but done through voice, such as a phone call
Impersonation: Which is done face to face and onsite
Smishing: This occurs through a text message
Millions of Dollars in Losses
So, how did a company lose millions in one communication? CSOOnline wrote about Ubiquiti a US Based company that was victim to a Social Engineering hack that cost them $39 Million USD.
This attack was perpetrated through email communication coming from a legitimate looking source to a decision maker in the finance team. The staff member was asked to transfer these funds to a legitimate looking customer account, only to fall victim to a very costly scam.
We've written an article about how Social Engineering has impacted some Australian Companies, targeting their CEO, click here to read more.
Don't become a victim
In order to stay ahead of this trend there are some steps that you can take to fortify your business environment.
- Take your time. Hackers want you to act first and think later. If the message conveys a sense of urgency, or uses high-pressure sales tactics be skeptical; never let urgency influence your careful review.
- Research. Be suspicious of any unsolicited messages. If the email looks like it is from a company you use, do your own research. Use a search engine to go to the real company’s site or locate a phone number and discuss with the person whom sent you the email.
- Delete any request for financial information or passwords. If you get asked to reply to a message with personal information, put simply, it's a scam.
- Reject requests for help or offers of help. Legitimate companies and organizations do not contact you to provide help. Similarly, if you receive a request for help from a charity or organization that you do not have a relationship with, delete it. To give, seek out reputable charitable organizations on your own to avoid falling for a scam.
- Don’t put a link in control of where you land. Stay in control by finding the website yourself using a search engine to be sure you land where you intend to land. Hovering over links in email will show the actual URL at the bottom.
- Consider Two-Factor Authentication
You should consider adopting an additional step of authentication for access to email accounts. Note, however, that this will only help in the cases in which the impersonators compromised an executive's email account, not when they spoofed the sender.When in doubt, your employees must ask themselves: Is this an email they were expecting? If the answer is "no," they should trust their gut and follow up on their instinct.
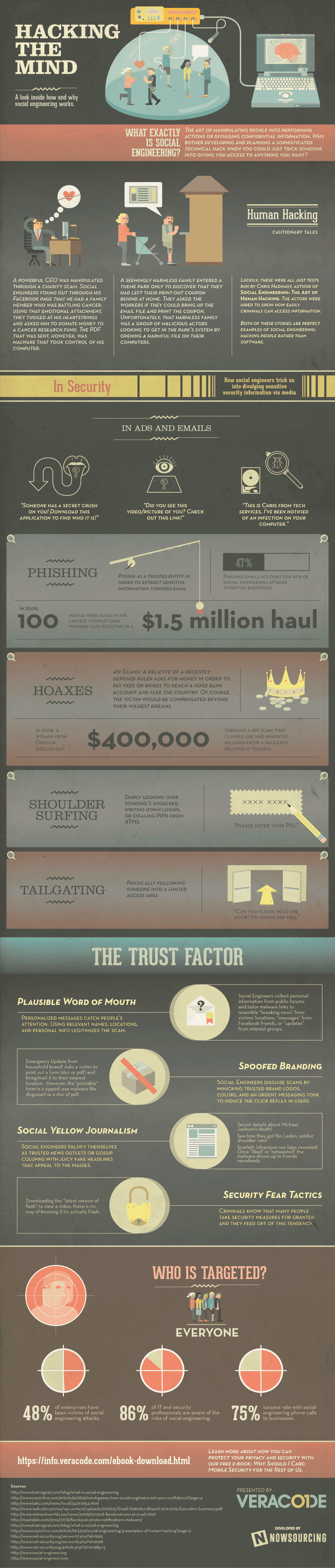
We’ve included a great infographic below from the team over at Veracode that helps to explain the complex idea that is social engineering.